The Emergence of Polymorphic Cyber Defense
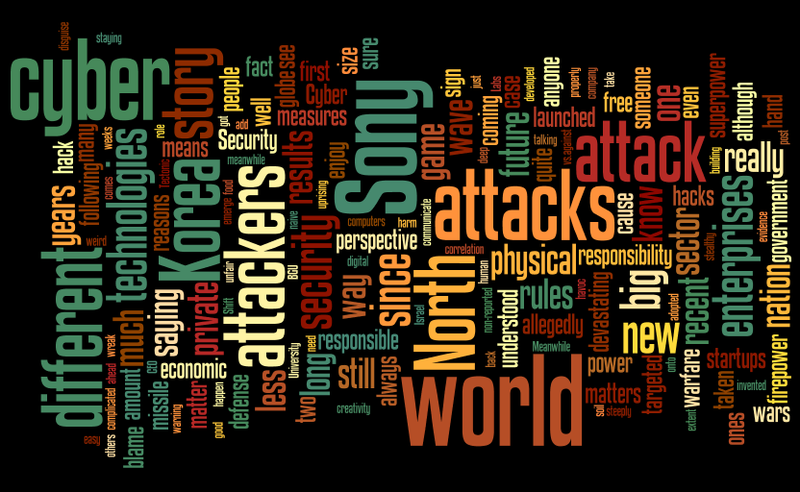
Background Attackers are Stronger Now The cyber-world is witnessing a fast-paced digital arms race between attackers and security defense systems, and 2014 showed everyone that attackers have the upper hand in this match.? Attackers are on the rise due to their growing financial interest?motivating a new level of sophisticated attacks that existing defenses are unmatched to combat. The fact that almost everything today is connected to the net and the ever-growing complexity of software and…